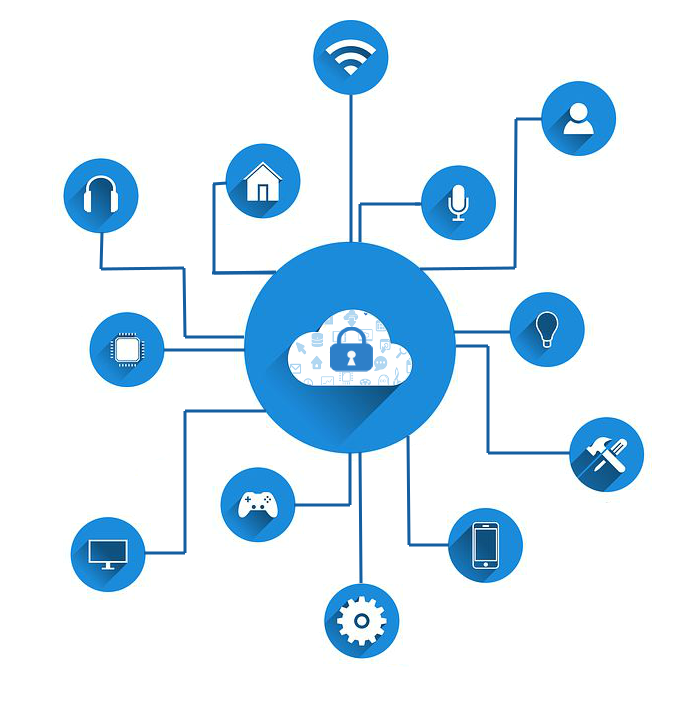
In the advent of modern technology, everything you do is recorded—where you go with your personal car, what you do with you personal computers and laptops at work, or which apps on your phone you frequently use. Every device you use that connects to the Internet, they create a network of mechanical and digital machines with unique identifiers that can share data over a network without the need of a man-to-man or man-to-computer interaction. This is the platform of IoT or Internet of things. To simply put, IoT refers to any tangible objects connected with the network.
In just a second, you can track the location of a lost vehicle or automate an entire building with it. To many business-oriented people, IoT also means opportunity for innovation and generating higher revenue since it is projected to grow significantly in the coming years as IoT delivers undeniable efficiency and customer satisfaction.
However, the immense proliferation of IoT platforms and their lack of security features introduce an enormous rise of security challenges. The bulging number of connected devices, applications, systems, and individuals indicates more avenue for exposure, and the higher the exposure, the higher the threat to security is.
Furthermore, data of these tangible physical items are stored in the cloud, which means that anyone, anywhere, can breach the access and gain relevant information that can cause an undesirable threat to a person, group, or state’s security.
IoT is a means of comfort but can be wrongly taken advantage by amateur hackers, petty cyber criminals, cyber espionage groups, terrorists, and state-sponsored attackers.
Considering the breadth of IoT platform, organizations will have to reinvent its scheme and integrate security programs to receive the rewards of the IoT itself. Hence, IoT security should be optimized.
The Levels of IoT Security
In its simplest sense, IoT security refers to securing the tangible objects connected with the network. The IoT security requires multi-level security methods that must impeccably coordinate with each other to deliver a holistic security solution from the device to the network and every process involved in the middle throughout the entire IoT security strategy.
The Device
The device must be equipped with security features both on the device’s hardware—the parts and materials of the product, and software—system programs running on the device. The hardware-based security feature is strong and fool-proof, which provides a more solid security foundation. Software-based IoT security feature mainly focused on the device’s program such as data at rest, device-unlocking, and face recognition.
Communication
IoT security concerns the mediums over which data is transferred or received. Unsecured transmission of data through the physical, network, or application channels can be gullible to intrusions while data is being delivered. Preemptive communication strategy of IoT security includes intrusion prevention system (IPS), intrusion detection system (IDS), system firewalls, data encryption, and access controls.
Cloud
IoT’s cloud is where data (often sensitive and personally identifiable information) from the IoT platforms are stored, examined, and interpreted to produce insights and perform actions to possible security threats. Cloud providers of IoT platforms are anticipated to offer secure and efficient cloud services to prevent major data breaches or downtime issues.
Life Cycle Management
Equipping security with IoT devices’ software and hardware, securing the transmission of data, and protecting the stored information in the cloud will never be enough to produce a complete and thorough IoT security without the sufficient and continuous procedure required. This involves the release of patches and updates of IoT software, assessment of risk and awareness, development of security policies and agreement, and extensive activity monitoring.
It is indeed imperative for today’s digital businesses to balance the benefits and liabilities that IoT platforms deliver through the use of IoT security. The device that efficiently helps on a daily basis is also the same device that attracts opportunities of breaches to security.